권호기사보기
| 기사명 | 저자명 | 페이지 | 원문 | 기사목차 |
|---|
결과 내 검색
동의어 포함
| 번호 | 참고문헌 | 국회도서관 소장유무 |
|---|---|---|
| 1 | McAfee Labs Threats Report, https://www. mcafee.com/enterprise/en-us/assets/reports/rp-quarterly-threats-aug-2019.pdf. (accessed January 6, 2020) | 미소장 |
| 2 | J. Kim, S. Hong, H. Kim, "A StyleGAN Image Detection Model Based on Convolutional Neural Network," Journal of Korea Multimedia Society, Vol. 22, No. 12, pp. 1447-1456, 2019 | 미소장 |
| 3 | T. Kim, H. Ji, and E. Im, “Malware Classification Using Machine Learning and Binary Visualization,” Korean Institute of Information Scientists Engineers Transactions on Compution Practices, Vol. 24, No. 4, pp. 198-203, 2018. | 미소장 |
| 4 | K. Han, B. Kang, and E. Im, “Malware Analysis Using Visualized Image Matrices,” The Scienti fic World Journal, Vol. 2014, Article ID. 132713, 2014. | 미소장 |
| 5 | Microsoft, Microsoft Malware Classification Challenge, https://www.kaggle.com/c/malwareclassification (accessed November 28, 2019). | 미소장 |
| 6 | S. Kang, N.V. Long, and S. Jung, “Android Malware Detection Using Permission-based Machine Learning Approach,” Journal of the Korea Institute of Information Security and Cryptology, Vol. 28, No. 3, pp. 617-623, 2018. | 미소장 |
| 7 | D. Jo and D. Park, “Real-time Malware Detection Method Using Machine Learning,”The Journal of Korean Institute of Information Technology, Vol. 16, No. 3, pp. 101-113, 2018. | 미소장 |
| 8 | J. Bae, C. Lee, S. Choi, and J. Kim, “Malware Detection Model with Skip-connected LSTM RNN,” The Korean Institute of Information Scientists and Engineers, Vol. 45, No. 12, pp. 1233-1239, 2018. | 미소장 |
| 9 | L. Nataraj, S. Karthikeyan, G. Jacob, and B. S. Manjunath, “Malware Images: Visualization and Automatic Classification,” Proceedings of the International Symposium on Visualization for Cyber Security, pp. 1-7, 2011. | 미소장 |
| 10 | W. Huang and J.W. Stokes, “MtNet: A Multi-Task Neural Network for Dynamic Malware Classification,” Proceedings of Detection of Intrusions and Malware, and Vulnerability Assessment, Vol. 9721, pp. 399-418, 2016. | 미소장 |
| 11 | S. Jeong, H. Kim, Y. Kim, and M. Yoon, “Vgram:Malware Detection Using Opcode Basic Blocks and Deep Learning,” Journal of Korean Institute of Information Scientists and Engineers, Vol. 46, No. 7, pp. 599-605, 2019. | 미소장 |
| 12 | M.S. Charikar, “Similarity Estimation Techniques from Rounding Algorithms,” Proceedings of the Thiry-fourth Annual ACM Symposium on Theory of Computing, pp. 380-388, 2002. | 미소장 |
| 13 | H. Kim, S. Han, S. Lee, and J. Lee, “Visualization of Malwares for Classification through Deep Learning,” Journal of Internet Computing and Services, Vol. 19, No. 5, pp. 67-75, 2018. | 미소장 |
| 14 | Anubis: Analyzing Unknown Binaries, https://www.virusbulletin.com/conference/vb 2009/abs tracts/anubis-analyzing-unknown-binariesautomatic-way (accessed January 10, 2020). | 미소장 |
| 15 | K. Han, J. Lim, and E. Im, “Malware Analysis Method Using Visualization of Binary Files,”Proceedings of the Research in Adaptive and Convergent Systems, pp. 317-321, 2013. | 미소장 |
| 16 | S. Seok and H. Kim, “Visualized Malware Classification Based-on Convolutional Neural Network,” Journal of the Korea Institute of Information Security and Cryptology, Vol. 26, No. 1, pp. 197-208, 2016. | 미소장 |
| 17 | S. Ni, Q. Qian, and R. Zhang, “Malware Identification Using Visualization Images and Deep Learning,” Computers and Security, Vol. 77, pp. 871-885, 2018. | 미소장 |
| 18 | J. Fu, J. Xue, Y. Wang, Z. Liu, and C. Shan, “Malware Visualization for Fine-grained Classification,” IEEE Access, Vol. 6, pp. 14510-14523, 2018. | 미소장 |
| 19 | H. Seo, J. Choi, and P. Chu, “A Study on Windows Malicious Code Classification System,”Journal of the Korea Society for Simulation, Vol. 18, No. 1, pp. 63-70, 2009. | 미소장 |
| 20 | Y. Jeon, J. Oh, I. Kim, and J. Jang, “A Study on Internet Malware Classification Method and Detection Mechanism,” Korea Institute of Information Security and Cryptology Review, Vol. 18, No. 3, pp. 60-73, 2008. | 미소장 |
| 21 | E. Raff, J. Barker, J. Sylvester, R. Brandon, B. Catanzaro, and C. Nicholas, “Malware Detection by Eating a Whole EXE,” Proceeding of American Association for Artificial Intelligence Workshop on AI for Cyber Security, pp. 268-276, 2018. | 미소장 |
*표시는 필수 입력사항입니다.
| 전화번호 |
|---|
| 기사명 | 저자명 | 페이지 | 원문 | 기사목차 |
|---|
| 번호 | 발행일자 | 권호명 | 제본정보 | 자료실 | 원문 | 신청 페이지 |
|---|
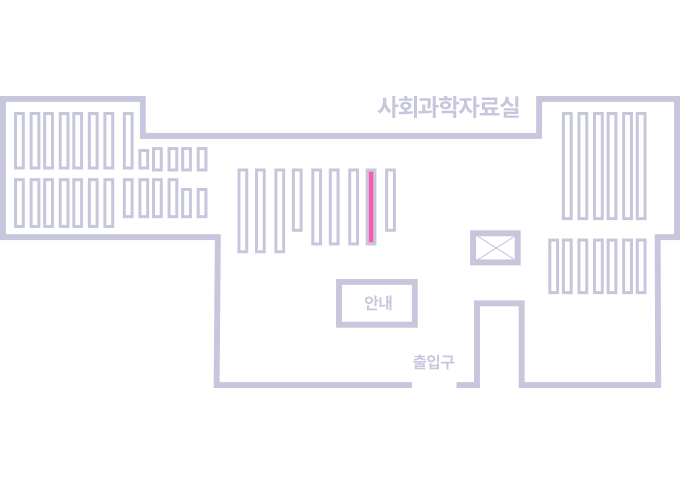
도서위치안내: / 서가번호:
우편복사 목록담기를 완료하였습니다.
*표시는 필수 입력사항입니다.
저장 되었습니다.