권호기사보기
| 기사명 | 저자명 | 페이지 | 원문 | 기사목차 |
|---|
결과 내 검색
동의어 포함
| 번호 | 참고문헌 | 국회도서관 소장유무 |
|---|---|---|
| 1 | C. Szegedy, W. Zaremba, and I. Suts kever, “Intriguing properties of neural networks.” International Conference o n Learning Representations (ICLR), 2014. | 미소장 |
| 2 | I. Goodfellow, J. Shlens, and C. Szege dy, “Explaining and harnessing advers arial examples.” International Confere nce on Learning Representations (ICL R), 2015. | 미소장 |
| 3 | N. Papernot, P McDaniel, and S. Jha et al., “The limitations of deep learnin g in adversarial settings” 2016 IEEE European symposium on security and privacy (EuroS&P), pp. 372-387, Mar. 2016. | 미소장 |
| 4 | S. Moosavi-Dezfooli, A. Fawzi, and P. Frossard, “DeepFool: a simple and acc urate method to fool deep neural net works” 2016 IEEE Conference on Com puter Vision and Pattern Recognition (CVPR), pp. 2574-2582, Jun 2016. | 미소장 |
| 5 | N. Carlini and D. Wagner, “Towards evaluating the robustness of neural n etworks.” 2017 IEEE Symposium on S ecurity and Privacy (SP), pp. 39-57, May 2017. | 미소장 |
| 6 | A. Athalye and I. Sutskever, “Synthes izing Robust Adversarial Examples,” I nternational Conference on Machine L earning (ICML), pp. 284-293, Jul. 2018. | 미소장 |
| 7 | A. Athalye, N. Carlini, and D. Wagne r, “Synthesizing Robust Adversarial E xamples” International Conference on Machine Learning (ICML), pp. 274-283, Jul. 2018. | 미소장 |
| 8 | J. Su and D. Vasconcellos et al., “On e pixel attack for fooling deep neural networks”, VOL. 23, NO. 5, pp. 828-841, Oct. 2019. | 미소장 |
| 9 | P. Chen, Huan Zhang, and Y. Sharma et al., “ZOO: Zeroth Order Optimizati on based Black-box Attacks to Deep Neural Networks without Training Su bstitute Models” 2017 ACM SIGSAC C onference on Computer and Communic ations Security, pp. 15-26, Nov. 2017. | 미소장 |
| 10 | N. Papernot, P. McDaniel, I. Goodfell ow et al. “Practical Black-Box Attacks against Machine Learning” 2017 ACM on Asia Conference on Computer and Communications Security, ASIA CCS’17, PP. 506-519, Apr. 2017. | 미소장 |
| 11 | W. Brendel, J. Rauber, and M. Bethg e, “Decision-Based Adversarial Attack s: Reliable Attacks Against Black-Box Machine Learning Models” Internation al Conference on Learning Representa tions, May 2018. | 미소장 |
| 12 | J. Chen, M. Jordan, and M. Wainwrig ht, “HopSkipJumpAttack: A Query-Efficient Decision-Based Attack” 2020 IE EE Symposium on Security and Priva cy (SP), pp. 1277-1294, May 2020. | 미소장 |
| 13 | N. Carlini and D. Wagner, “Audio Adv ersarial Examples: Targeted Attacks on Speech-to-Text” 2018 IEEE Securit y and Privacy Workshops (SPW), pp. 1-7, May 2018. | 미소장 |
| 14 | M. Alzantot, B. Balaji, and M. Srivas tava, “Did you hear that? Adversarial Examples Against Automatic Speech Recognition” Machine Deception Work shop, Neural Information Processing Systems (NIPS), 2017. | 미소장 |
| 15 | R. Taori, A. Kamsetty, and B. Chu et al.,“Targeted Adversarial Examples for Black Box Audio Systems” 2019 IEEE Security, and Privacy Workshops (SP W), pp. 15-20, May 2019. | 미소장 |
| 16 | X. Yuan, Y. Chen, and Y. Zhao et al., “Commandersong: A systematic appro ach for practical adversarial voice rec ognition” 27th USENIX Security Symp osium, pp. 49-64, Aug. 2018. | 미소장 |
| 17 | C. Kereliuk, B. L. Sturm, and J. Lars en, “Deep Learning and Music Advers aries,” IEEE Transactions on Multime dia, vol. 17, no. 11, pp. 2059-2071, No v. 2015. | 미소장 |
| 18 | H. Abdullah, W. Garcia, and C. Peete rs et al., “Practical hidden voice attac ks against speech and speaker recogni tion systems” NDSS 2019, pp. 1369–1378, 2019. | 미소장 |
| 19 | L. Schonherr, K. Kohls, and S. Zeiler et al., “Adversarial Attacks Against A utomatic Speech Recognition Systems via Psychoacoustic Hiding” NDSS 2019. | 미소장 |
| 20 | H. Yakura and J. Sakuma, “Robust A udio Adversarial Example for a Physic al Attack” 28th International Joint Co nference on Artificial Intelligencepp. 5334-5341, 2019. | 미소장 |
| 21 | S. Hu, X. Shang, and Z. Qin et al., “Adversarial Examples for Automatic Speech Recognition: Attacks and Cou ntermeasures” IEEE Communications Magazine, pp. 120-126, Oct. 2019 | 미소장 |
| 22 | Simple audio recognition: Recognizing keywords. Accessed: September 13, 20 21. [Online]. Available: https://www. tensorflow.org/tutorials/audio/simple_audio | 미소장 |
| 23 | P. Warden “Speech Commands: A Dat aset for Limited-Vocabulary Speech R ecognition” arXiv preprint arXiv:1804. | 미소장 |
*표시는 필수 입력사항입니다.
| 전화번호 |
|---|
| 기사명 | 저자명 | 페이지 | 원문 | 기사목차 |
|---|
| 번호 | 발행일자 | 권호명 | 제본정보 | 자료실 | 원문 | 신청 페이지 |
|---|
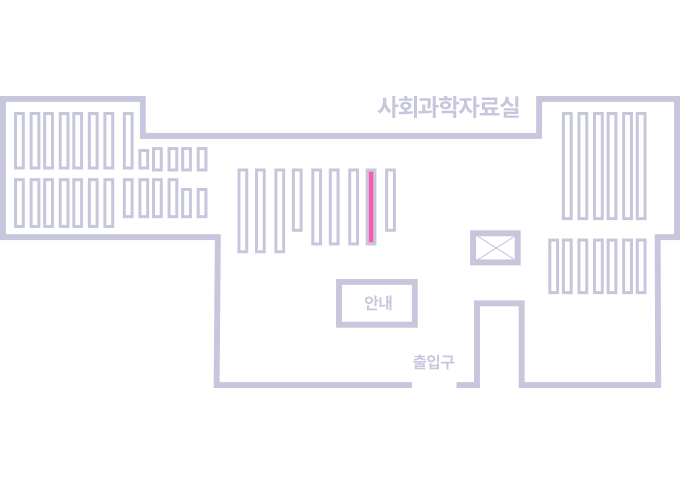
도서위치안내: 정기간행물실(524호) / 서가번호: 국내09
2021년 이전 정기간행물은 온라인 신청(원문 구축 자료는 원문 이용)
우편복사 목록담기를 완료하였습니다.
*표시는 필수 입력사항입니다.
저장 되었습니다.