권호기사보기
| 기사명 | 저자명 | 페이지 | 원문 | 기사목차 |
|---|
결과 내 검색
동의어 포함
Title Page
Contents
Abstract 9
I. Introduction 13
II. Related work 18
A. Named Data Networking (NDN) 18
B. Name Prefix Trie (NPT) 24
C. Bloom Filter 30
D. Counting Bloom Filter (CBF) 37
E. Name Prefix Trie with a Bloom Filter (NPT-BF) 39
III. Proposed Bloom Filter Structure 46
A. Ternary Bloom Filter (TBF) 46
B. Analysis 49
1. Negative 50
2. Indeterminable 51
3. False positive 51
4. Undeletable 52
C. Performance Evaluation 53
IV. Proposed Name Prefix Lookup Algorithms 60
A. Path Compression Name Prefix Trie (PC-NPT) 60
B. Path Compression Name Prefix Trie with a Skip Bloom Filter (PC-NPT-SBF) 67
C. Path Compression Name Prefix Trie with Quarternary Bloom Filter (PC-NPT-QBF) 80
D. Performance Evaluation 86
V. Conclusion 99
REFERENCES 102
국문초록 113
Figure 1. Current Internet and NDN protocol stack 19
Figure 2. NDN packet types 20
Figure 3. NDN forwarding engine model 21
Figure 4. Forwarding process at an NDN 22
Figure 5. Name prefix trie (NPT) 25
Figure 6. Example of NPT building procedure 26
Figure 7. NPT search procedure 27
Figure 8. Initialized Bloom Filter 32
Figure 9. Programming of Bloom filter 32
Figure 10. Bloom filter produces a positive result 34
Figure 11. Bloom filter produces a negative result 34
Figure 12. Bloom filter produces a false positive result 35
Figure 13. Counting Bloom Filter (CBF) 37
Figure 14. Name prefix trie with a Bloom filter (NPT-BF) 40
Figure 15. Proposed ternary Bloom filter (TBF) 47
Figure 16. Probability of indeterminable 56
Figure 17. Probability of undeletable 58
Figure 18. Probability of false positive 59
Figure 19. Example of the removable nodes in an NPT 62
Figure 20. Proposed path-compression name prefix trie (PC-NPT) 63
Figure 21. Search procedure for PC-NPT 64
Figure 22. Flow chart of search procedure of PC-NPT 66
Figure 23. Phase 1 programming process of PC-NPT-SBF 68
Figure 24. Phase 2 programming process of PC-NPT-SBF 69
Figure 25. Phase 2 programming process of PC-NPT-SBF... 70
Figure 26. Proposed PC-NPT with skip Bloom filter (PC-NPT-SBF) 71
Figure 27. Phase 1 querying process of PC-NPT-SBF 73
Figure 28. Phase 2 querying of PC-NPT-SBF 74
Figure 29. Phase 1 querying of PC-NPT-SBF (school) 75
Figure 30. Flow chart of search procedure of PC-NPT-SBF 76
Figure 31. Number of skip nodes for each level (10k) 78
Figure 32. Number of skip nodes for each level (50k) 78
Figure 33. Number of skip nodes for each level (100k) 79
Figure 34. Phase 1 programming process of PC-NPT-QBF 81
Figure 35. Phase 2 programming process of PC-NPT-QBF 82
Figure 36. Proposed PC-NPT-QBF 83
Figure 37. Flow chart of search procedure of PC-NPT-QBF 85
Figure 38. Number of skip nodes divided by number of total nodes 91
Figure 39. Comparison of the average number of node accesses 96
Figure 40. Worst-case number of node accesses 96
Figure 41. Probability of false positive of PC-NPT-SBF 98
*표시는 필수 입력사항입니다.
| 전화번호 |
|---|
| 기사명 | 저자명 | 페이지 | 원문 | 기사목차 |
|---|
| 번호 | 발행일자 | 권호명 | 제본정보 | 자료실 | 원문 | 신청 페이지 |
|---|
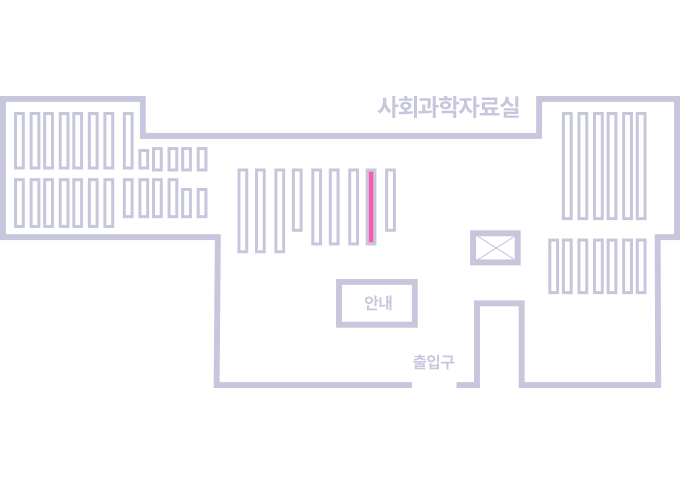
도서위치안내: / 서가번호:
우편복사 목록담기를 완료하였습니다.
*표시는 필수 입력사항입니다.
저장 되었습니다.