권호기사보기
| 기사명 | 저자명 | 페이지 | 원문 | 기사목차 |
|---|
결과 내 검색
동의어 포함
| 기사명 | 저자명 | 페이지 | 원문 | 목차 |
|---|---|---|---|---|
| The Development of SP Security Functional Requirements in CMVP | 문길종, 고갑승, 류동주 | pp.657-664 |
|
|
| 스마트폰에서의 콘텐츠 보안 연구 | 성정숙 | pp.665-672 |
|
|
| 수배전반 시스템의 신뢰성 향상을 위한 오류 예측 시스템 | 조상영 | pp.705-714 |
|
|
| CC 3.1 기반 무선위협관리시스템(AIRTMS V1.0) 보안기능요구사항 개발 | 고갑승, 문길종, 류동주 | pp.645-656 |
|
|
| SW공학 표준 커리큘럼에 관한 연구 | 염희균, 황선명 | pp.693-704 |
|
|
| ESCORT : Secure P2P Protocol for Global Cooperation in Overlay Network Services | 서대희, 안개일, 김종현, 조동섭, 백장미 | pp.673-692 |
|
*표시는 필수 입력사항입니다.
| 전화번호 |
|---|
| 기사명 | 저자명 | 페이지 | 원문 | 기사목차 |
|---|
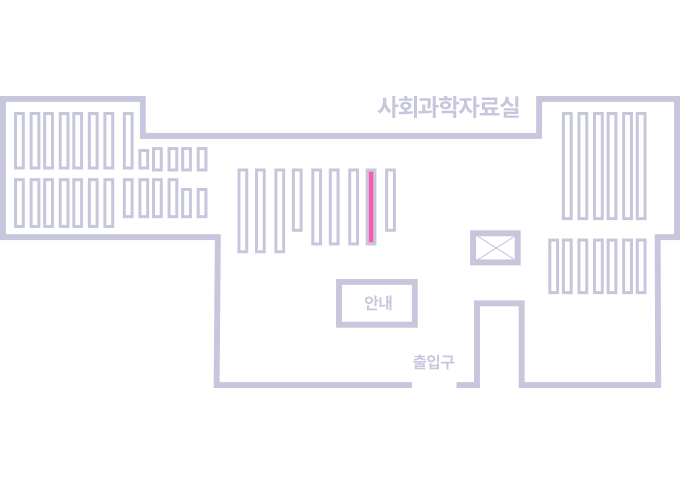
| 번호 | 발행일자 | 권호명 | 제본정보 | 자료실 | 원문 | 신청 페이지 |
|---|
도서위치안내: / 서가번호:
우편복사 목록담기를 완료하였습니다.
*표시는 필수 입력사항입니다.
저장 되었습니다.