권호기사보기
| 기사명 | 저자명 | 페이지 | 원문 | 기사목차 |
|---|
결과 내 검색
동의어 포함
RSA signature algorithms using the Chinese remaindertheorem (CRT-RSA) are approximately four-times fasterthan straightforward implementations of an RSAcryptosystem. However, the CRT-RSA is known to bevulnerable to fault attacks; even one execution of thealgorithm is sufficient to reveal the secret keys. Over thepast few years, several countermeasures against CRT-RSAfault attacks have tended to involve additionalexponentiations or inversions, and in most cases, they arealso vulnerable to new variants of fault attacks. In thispaper, we review how Shamir’s countermeasure can bebroken by fault attacks and improve the countermeasureto prevent future fault attacks, with the added benefit oflow additional costs. In our experiment, we use the sidechannelanalysis resistance framework system, a faultinjection testing and verification system, which enables usto inject a fault into the right position, even to within 1 μs.
We also explain how to find the exact timing of the targetoperation using an Atmega128 software board.| 번호 | 참고문헌 | 국회도서관 소장유무 |
|---|---|---|
| 1 | Differential Fault Analysis for Round‐Reduced AES by Fault Injection | 소장 |
| 2 | J. Blomer, M. Otto, and J.-P. Seifert, “A New CRT-RSA Algorithm Secure Against Bellcore Attacks,” Tenth ACM Conf. Comput. Commun. Security, Washington, DC, USA, Oct. 27–30, 2003, pp. 311–320. | 미소장 |
| 3 | J. Blomer and M. Otto, “Wagner’s Attack on a Secure CRT-RSA Algorithm Reconsidered,” Third Int. Conf. Fault Diagnosis Tolerance Cryptography, Yokohama, Japan, 2006, pp. 13–23. | 미소장 |
| 4 | C. Aumuller et al., “Fault Attacks on RSA with CRT: Concrete Results and Practical Countermeasures,” Cryptographic Hardware Embedded Syst., Redwood Shores, CA, USA, Aug. 13–15, 2002, pp. 260–275. | 미소장 |
| 5 | A. Boscher, H. Handschuh, and E. Trichina, Fault Resistant RSA Signatures: Chinese Remaindering in Both Directions. Accessed Mar. 31, 2014. http://eprint.iacr.org/2010/038 | 미소장 |
| 6 | D. Vigilant, “RSA with CRT: A New Cost-Effective Solution to Thwart Fault Attacks,” Tenth Int. Conf. Cryptographic Hardware Embedded Syst., Washington, DC, USA, Aug. 10–13, 2008, pp. 130–145. | 미소장 |
| 7 | RSA speedup with Chinese remainder theorem immune against hardware fault cryptanalysis  |
미소장 |
| 8 | D. Wagner, “Cryptanalysis of a Provably Secure CRT-RSA Algorithm,” Eleventh ACM Conf. Comput. Commun. Security, Washington, DC, USA, Oct. 25–29, 2004, pp. 92–97. | 미소장 |
| 9 | S.-K. Kim et al., “An Efficient CRT-RSA Algorithm Secure against Power and Fault Attacks,” J. Syst. Software, vol. 84, no. 10, Oct. 2011, pp. 1660–1669. | 미소장 |
| 10 | S.-M. Yen, D. Kim, and S.J. Moon, “Cryptanalysis of Two Protocols for RSA with CRT Based on Fault Infection,” Third Int. Conf. Fault Diagnosis Tolerance Cryptography, Yokohama, Japan, vol. 4236, 2006, pp. 53–61. | 미소장 |
| 11 | J.-S. Coron et al., “Fault Attacks and Countermeasures on Vigilant’s RSA-CRT Algorithm,” Seventh Int. Conf. Fault Diagnosis Tolerance Cryptography, Santa Babara, CA, USA, Aug. 21, 2010, pp. 89–96. | 미소장 |
| 12 | D. Boneh, R.A. DeMillo, and R.J. Lipton, “On the Importance of Checking Cryptographic Protocols for Faults,” Advances in Cryptology Sixteenth Annual Int. Conf. Theory Appl. Cryptographic Tech., Konstanz, Germany, May 11–15, 1997, pp. 37–51. | 미소장 |
| 13 | A. Shamir, Improved Method and Apparatus for Protecting Public Key Schemes from Timing and Fault Attacks, US Patent 5,991,415, filed May 12, 1997, issued Nov. 23, 1999. | 미소장 |
| 14 | C. Giraud, “An RSA Implementation Resistant to Fault Attacks and to Simple Power Analysis,” IEEE Trans. Comput., vol. 55, no. 9, Sept. 2006, pp. 1116–1120. | 미소장 |
| 15 | S.-M. Yen et al., “RSA Speedup with Residue Number System Immune against Hardware Fault Cryptanalysis,” Fourth Int. Conf. Info. Security Cryptology, Seoul, Rep. of Korea, Dec. 6–7, 2001, pp. 397–413. | 미소장 |
| 16 | S.-K. Kim et al., “An Efficient CRT-RSA Algorithm Secure against Power and Fault Attacks,” J. Syst. Softw., vol. 84, no. 10, Oct. 2011, pp. 1660–1669. | 미소장 |
| 17 | A. Boscher, R. Naciri, and E. Prouff, “CRT RSA Algorithm Protected against Fault Attacks,” First Workshop Info. Security Theory Practice, Crete, Greece, May 9–11, 2007, pp. 229–243. | 미소장 |
| 18 | M. Ciet and M. Joye, “Practical Fault Countermeasures for Chinese Remaindering Based RSA,” Second Int. Conf. Fault Diagnosis Tolerance Cryptography, Scotland, UK, Sept. 2, 2005, pp. 124–131. | 미소장 |
| 19 | ISO 7816, “Identification Cards Integrated Circuit(s) Cards with Contacts,” Geneva, Switzerland, Created in 1989, amended in 1992. | 미소장 |
| 20 | Atmega 128 specification. Accessed Mar. 31, 2014. http://www. atmel.com/Images/doc2467.pdf | 미소장 |
*표시는 필수 입력사항입니다.
| 전화번호 |
|---|
| 기사명 | 저자명 | 페이지 | 원문 | 기사목차 |
|---|
| 번호 | 발행일자 | 권호명 | 제본정보 | 자료실 | 원문 | 신청 페이지 |
|---|
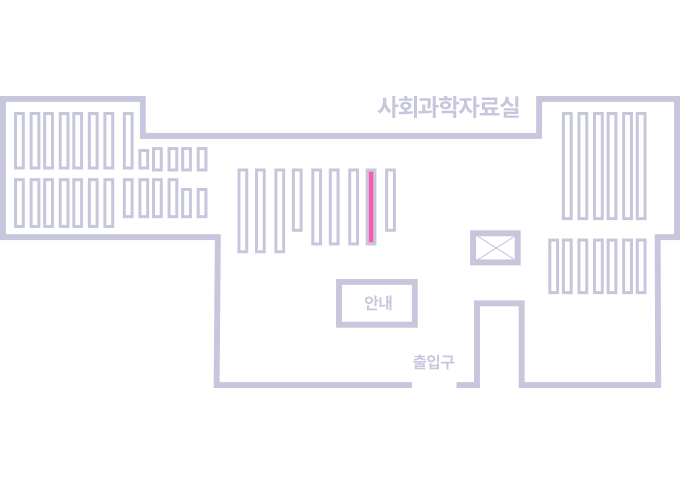
도서위치안내: 정기간행물실(524호) / 서가번호: 국내17
2021년 이전 정기간행물은 온라인 신청(원문 구축 자료는 원문 이용)
우편복사 목록담기를 완료하였습니다.
*표시는 필수 입력사항입니다.
저장 되었습니다.