권호기사보기
| 기사명 | 저자명 | 페이지 | 원문 | 기사목차 |
|---|
결과 내 검색
동의어 포함
컴퓨터 기술의 급속한 발전은 더 안전한 사용자 환경이 필요하게 되어, 모든 내부 및 외부 네트워크 활동을 검증하는 제로 트러스트 모델의 도입을 촉진했다. 본 논문은 제로 트러스트의 구현 및 지연 문제를 해결하기 위해 소프트웨어 정의 경계 기능을 활용한 효율적인 네트워크 트래픽 데이터 기반 동적 접근 제어 방법을 제안한다. 성능 평가 결과에 따르면 제안한 방법의 탐지 성능은 기존 방식과 유사하게 나타났지만 데이터 셋의 크기는 약 70% 감소했다. 그리고 적응형 제로 트러스트 검증 방식을 제안하여 데이터 셋 크기와 검증 시간을 각각 약 83%, 10% 줄이면서 종래의 방식과 유사한 탐지 성능을 유지했다.
The rapid advancement of computer technology has necessitated a safer user environment, prompting the adoption of the zero trust model, which verifies all internal and external network activities. This paper proposes an efficient network traffic data-based dynamic access control method leveraging Software-Defined Perimeter (SDP) capabilities to implement zero trust and address latency issues. According to the performance evaluation results, the detection performance of the proposed scheme is similar to that of conventional schemes, but the dataset size was reduced by 62.47%. Additionally, by proposing an adaptive zero trust verification approach, the dataset size and verification time were reduced by 83.9% and 9.1%, respectively, while maintaining similar detection performance to conventional methods.| 번호 | 참고문헌 | 국회도서관 소장유무 |
|---|---|---|
| 1 | Syed, N. F., Shah, S. W., Shaghaghi, A., Anwar, A., Baig, Z., & Doss, R., "Zero trust architecture (zta): A comprehensive survey," IEEE Access, Volume: 10, pp.57143-57179, 12 May 2022. | 미소장 |
| 2 | Teerakanok, S., Uehara, T., Inomata, A., "Migrating to zero trust architecture: Reviews and challenges,"Security and Communication Networks, pp. 1-10, 25 May 2021 | 미소장 |
| 3 | TN, N., Pramod, D., Singh, R., "Zero trust security model: Defining new boundaries to organizational network,"In Proceedings of the 2023 Fifteenth International Conference on Contemporary Computing, pp. 603-609, August. 2023 | 미소장 |
| 4 | So-Hui Kim, Il-Gu Lee, Ye-Eun Lee, "Practical Zero Trust Technology and Policy for 5G Network Convergence Industry," Korean Journal of Industrial Security, Vol. 14, pp.203-222, Jan. 2024 | 미소장 |
| 5 | Fernandez, Eduardo B., and Andrei Brazhuk, "A critical analysis of Zero Trust Architecture (ZTA)," Computer Standards & Interfaces, volume: 89, 103832, April. 2024 | 미소장 |
| 6 | Zolotukhin, M., Hämäläinen, T., &Kotilainen, P., "Intelligent solutions for attack mitigation in zero-trust environments. In Cyber Security:Critical Infrastructure Protection", Cham: Springer International Publishing, COMPUTMETHODS, volume 56, pp. 403-417, 2022 | 미소장 |
| 7 | S. Rose, O. Borchert, S. Mitchell, S. Connelly, "Zero Trust Architecture,"NIST Special Publication 800-207, National Institute of Standards and Technology, U.S. Department of Commerce, August 2020. | 미소장 |
| 8 | Park, C. S., "Zero Trust Architecture."Review of Korea Institute of Information Security and Cryptology (KIISC), volume. 33, No. 4, pp.131-141, August 2023 | 미소장 |
| 9 | Lee. J. Y, Choi. B. H, Koh. N, Chun. S, "A Study on the Establishment of Zero Trust Security Model," Korea Information Processing Society/Computer and Communication System, volume: 12, No. 6, pp. 189-196, June 2023 | 미소장 |
| 10 | Devarakonda, A., Sharma, N., Saha, P., & Ramya, S., "Network intrusion detection: A comparative study of four classifiers using the NSL-KDD and KDD’99 datasets," In Journal of Physics: Conference Series, IOP Publishing, Vol. 2161, No. 1, p. 012043, 2022 | 미소장 |
| 11 | Yao, Q., Wang, Q., Zhang, X., Fei, J., "Dynamic access control and authorization system based on zerotrust architecture," In Proceedings of the 2020 1st international conference on control, robotics and intelligent system, pp. 123-127, October. 2020 | 미소장 |
| 12 | Jin, Q., Wang, L., "Zero-trust based distributed collaborative dynamic access control scheme with deep multi-agent reinforcement learning,"EAI Endorsed Transactions on Security and Safety, 27 August 2022 | 미소장 |
| 13 | Jeon, So-Eun, et al. "Suboptimal Feature Selection Techniques for Effective Malicious Traffic Detection on Lightweight Devices." CMESComputer Modeling in Engineering &Sciences, 140(2), May. 2024 | 미소장 |
| 14 | Gouveia, A., Correia, M., "Network intrusion detection with XGBoost," In Recent Advances in Security, Privacy, and Trust for Internet of Things (IoT)and Cyber-Physical Systems (CPS), Chapman and Hall/CRC, pp. 137-166, 2020 | 미소장 |
| 15 | Deng, Y., Lumley, T, "Multiple imputation through xgboost", Journal of Computational and Graphical Statistics, volume: 33, No: 2 pp.1-19, October. 2023 | 미소장 |
| 16 | M. Tavallaee, E. Bagheri, W. Lu, and A. Ghorbani, “A Detailed Analysis of the KDD CUP 99 Data Set,” 2009IEEE symposium on computational intelligence for security and defense applications (CISDA), p. 1-6, July. 2009 | 미소장 |
| 17 | Iman Sharafaldin, Arash Habibi Lashkari, and Ali A. Ghorbani, “Toward Generating a New Intrusion Detection Dataset and Intrusion Traffic Characterization”, 4th International Conference on Information Systems Security and Privacy (ICISSP), Portugal, January 2018 | 미소장 |
*표시는 필수 입력사항입니다.
| 전화번호 |
|---|
| 기사명 | 저자명 | 페이지 | 원문 | 기사목차 |
|---|
| 번호 | 발행일자 | 권호명 | 제본정보 | 자료실 | 원문 | 신청 페이지 |
|---|
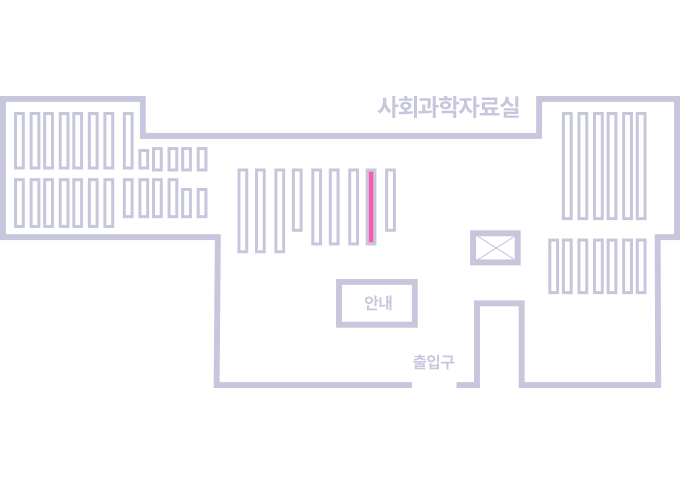
도서위치안내: 정기간행물실(524호) / 서가번호: 국내09
2021년 이전 정기간행물은 온라인 신청(원문 구축 자료는 원문 이용)
우편복사 목록담기를 완료하였습니다.
*표시는 필수 입력사항입니다.
저장 되었습니다.